WordPress is the choice of many for setting up their website. Site security measures are therefore one of the most discussed subjects in the WP community.
Security can be addressed through simple steps like changing the admin user name to more complex measures such as specialized security plugins. Regardless of all this, websites get hacked every day. It is very important to secure one’s website and equally important to identify any hacking at the earliest.
Malware can grant access to your system and compromise the security and health of your WordPress website. It is spurious in nature. This is where malware scanners come in. Malware scanners offer protection by scanning, detecting and removing malware.
Most scanners have an inbuilt malware database with file definitions and actions. This helps in malware detection. If a match is found with a file in the scanner database, the scanner will single it out and act upon it. In cases where the malware cannot be removed by the scanner the malware scanner will quarantine the malware.
Three of the most popular WordPress malware scanner plugins are Sucuri Security, Exploit Scanner and Wordfence Security.
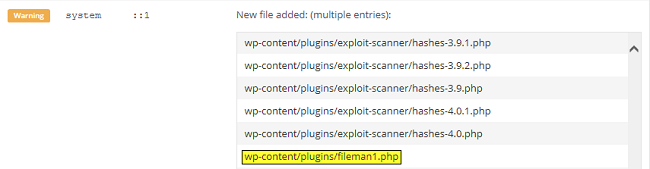
I tried out all three. The real test of effectiveness of a malware scanner is in its ability to identify real malware. Since the test website I am installed these malware scanners has a fresh installation of WordPress, I manually introduced two different types of malware files into my website entitled bastian.php and fileman1.php. You can read more about the type of scripts I added to these files in this article.
Sucuri Security
Sucuri Security was the only plugin I installed that prodded me for the API key generation.
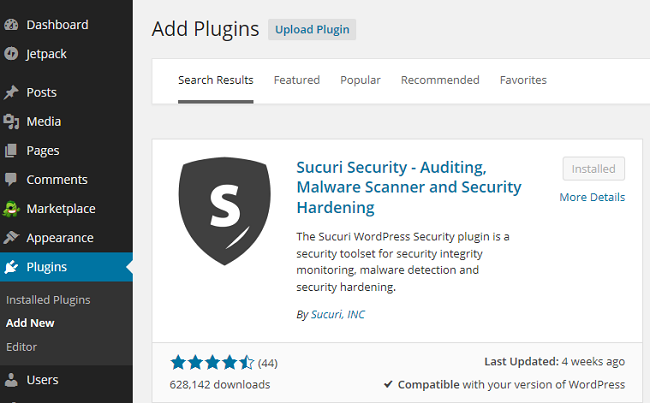
The free plugin offers a basic service to check if your website is ok. I clicked on the Scan tab and the scan was completed in seconds. To my surprise, the scan did not detect either of the two. I looked around for a bit but it seemed like Sucuri had given my site and its contents a clean bill of health.
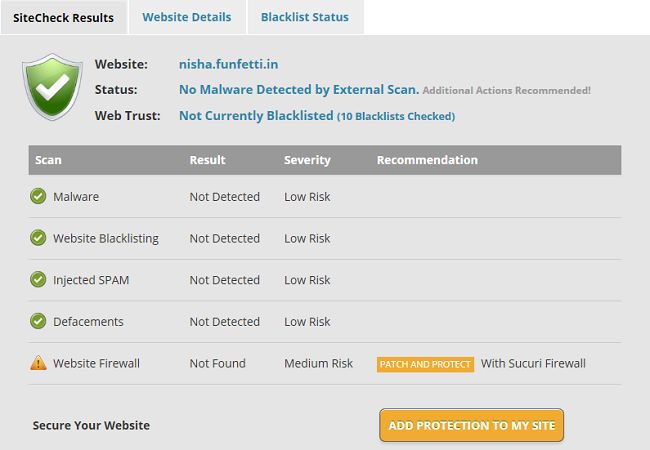
It was a bit of a let down, since both the files were showing in the audit logs in the background page.
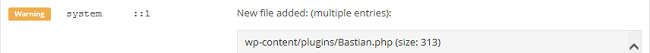
With an ambiguous message about possible file and folder modifications in the mauve box, Sucuri is safely sitting on the fence. The message that I got was to manually check the folders in the specified locations for this scan to be sure that there was an issue.
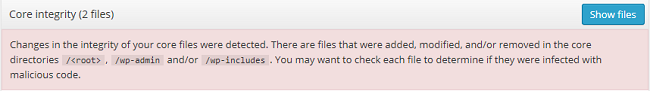
I installed the scanner to sort the issue. Manual checking is always an option, but usually the last one. While it is nice to see changes being highlighted, I would rather the scanner show me what the issue is and where the issue is. And I would rather it showed me how to resolve the issue rather than suggesting a manual check.
Moving on, I installed a plugin from WordPress that was malware free. After activating it, I ran the Sucuri scan again.
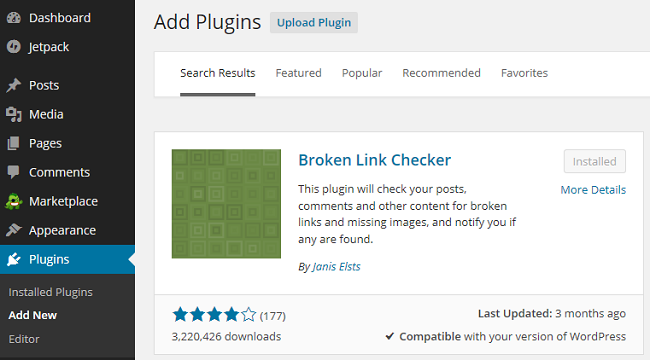
I was given a clean sheet this time as well, but I saw a pattern that any new installation gets an orange Warning box from Sucuri.
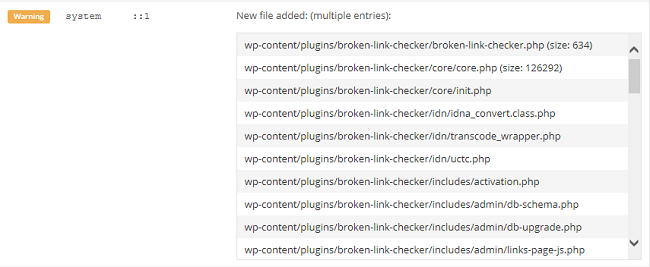
This is very similar to the mail alerts that Sucuri sends every time I log in and customize my website. I found the Sucuri free scanner performance pretty dismal.
After some more looking around, I found this:
There was a bouquet of services on offer. These are, however, available at a price. My guess is that there may be value in the paid options since they offer a firewall, IP blocking, post–hack, and the works. Sucuri security and the various services provided are cloud based and general reviews about the paid version are positive.
Exploit Scanner
This scanner took the longest time to scan but returned with a check of 399 odd files. A whole lot of strings were displayed which made zero sense to me.
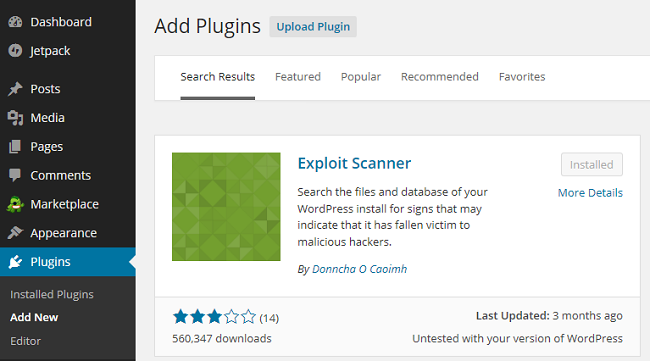
I did not see anything malicious in my scan. Most searches described unknown files. It made me feel good that there was such thorough checking.
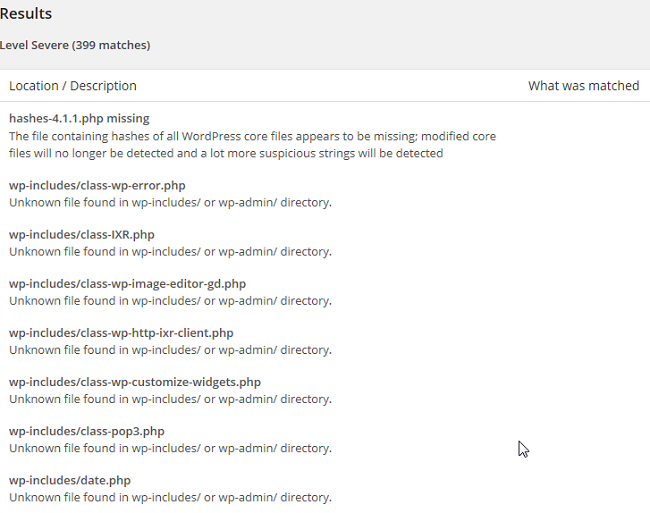
My initial joy soon gave way to disappointment. This scanner showed me 399 files which had nothing, but did not show me the two files that I knew were infected. Repeated checking of so many files, if anything, can lead to manual error since overlooking in such cases is natural.
To sum up, Sucuri and Exploit scanners seem pretty much the same to me except for the fact that the latter was quite comprehensive in its results. Neither of them were helpful in my case though.
Wordfence Security
The reviews I had read for Wordfence Security were really good, but I was keen to see all of it for myself.
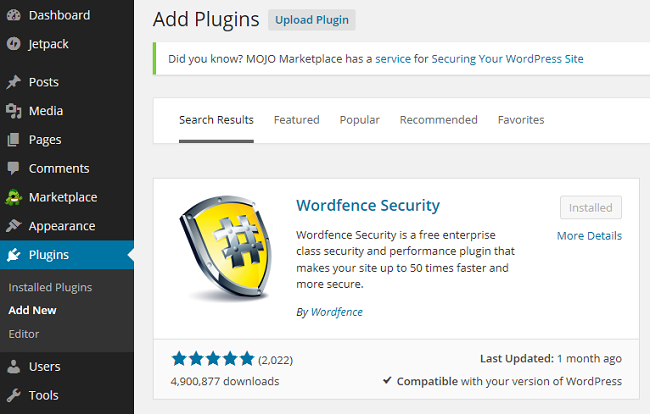
As soon as I installed this plugin, I got a pop up asking for my email ID so that I could receive security alerts. There are plenty of other options to choose from the menu, but you need to pay for some features such as scan scheduling.

Wordfence is a bit of an all-rounder, but does not have any options to scan themes or plugins, which is is contrast to Exploit Scanner which scans everything.
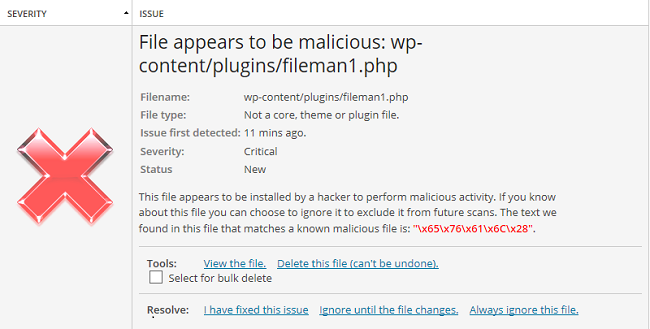
After the scan, I received an email from Wordfence pointing out issues found on my site.
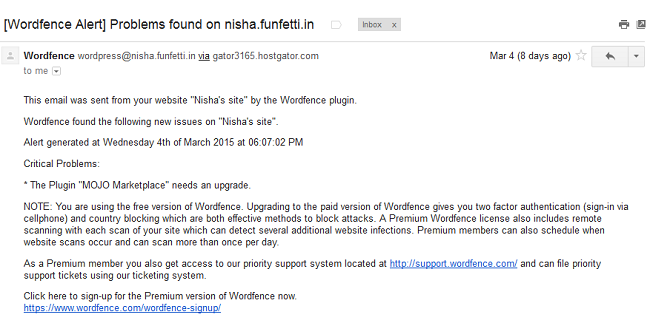
I found Wordfence Security to be the best solution out of the three I tested, however I was still not 100% happy with the results.
Conclusion
Sucuri Security, Exploit Scanner and Wordfence Security, while bringing the various apparent issues to the fore, did not quarantine any questionable file. The onus of removing any suspicious file is on the person maintaining the website.
One thing is clear: There are no foolproof scanners for WordPress. Even if I were to pay for premium features, the question of how secure my website really is will always remain open ended.
Given the choices that I have now tested, Wordfence Security is undoubtedly my preferred WordPress malware scanner, however I recommend testing your website using multiple scanners from time to time to help you detect malicious files.
Nisha
Featured Image Credit: “Padlock” by Alyson Hurt from Alexandria, Va., USA – Flickr. Licensed under CC BY 2.0 via Wikimedia Commons.

